| |
| Recover Windows Passwords Using Rainbow Crack |
|
|
|
|
|
|
|
| |
| |
|
Gone are the days when we have to wait for the days together to
recover the Windows account password. Thanks to the
rainbow crack
technology, now we can crack the passwords in few seconds
with 100% success rate.
This Rainbow cracking technology works on simple concept. Instead of
computing the hashes for each password dynamically and comparing with
the correct one during cracking, password hashes are computed
in advance for all character sets. These hashes are then stored in
datasets called rainbow tables.
So cracking involves just comparing the current password hash with
the pre computed
hashes within the rainbow tables and get the associated plain text
password. Hence it takes very less time
compared to the traditional method of brute force cracking. Setting up the
rainbow table for various character sets is just one time activity and
may take days or months based on the character set and
speed of the machine. Once the rainbow tables are ready, you can feed
the password hash to it and get your password cracked in seconds. |
|
 |
| |
| |
|
In order to recover your Windows user password,
first you have to get the
LM hash for the target user account. This can be done in many ways. You can
use any of the tools such as
pwdump,
cain&abel or
LC5. You
need to have administrator privileges to dump the hashes using these
tools. If you
have lost administrator password itself, then you can boot the
system using
BackTrack live cd or Windows restore CD and then copy the SAM &
SYSTEM hive files (which is located in c:\windows\system32\config
folder. Note that your system drive may be different). Next feed these
files to Cain
& Abel tool to get the LM hashes for the target account. |
|
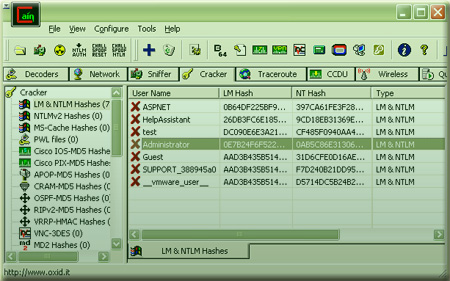
| Here is the screenshot of retrieving LM hash for users using the
Cain&Abel tool |
|
 |
|
Once you have collected the LM
password hash, you can start the password cracking operation using
the rcrack tool (part of the
RainbowCrack Project)
with the rainbow tables that you have already created for certain
character sets.
|
|
| Note that with Vista onwards Windows no longer stores LM hashes
(unless under certain configurations) as it was susceptible to
easy brute force cracking. In such cases, you can as well use the NTLM
hash to recover password with RainbowCrack. |
|
| Ideally setting up the rainbow tables takes huge amount of disk space
and lot of computing time to generate the tables. Hence its not
practical for anyone to create such an setup on the home system. |
| |
| |
|
To make the game eaiser, lot of websites ( including free as
well as commericial ) offer free online rainbow cracking service. These
organizations have setup huge database of rainbow tables for all keysets
on their high end machines which makes the cracking possible in few
seconds. Also these services offer password cracking for different type
of hashes such as LM, NTLM, SHA, MD5 etc.
For FREE services you may have to wait for some time based on the load
and incoming requests. However you may also look for commercial services
for quick results at smaller cost.
If you are an organization who needs this kind of password
recovery service frequently then you can consider buying precomputed rainbow
tables for reasonable price and perform the password cracking operation using
rcrack tool. |
|
|
|
|
| If you find good online hash cracker links let us know, we will
update it here. |
|
| Now you don't have to wait for days together with half hope to get
back your lost password :) |
| |
| |
|
| 1. RainbowCrack:
Fast method of recovering Windows password. |
| 2. pwdump: Tool to dump
hashes of Windows user accounts. |
| 3. Cain & Abel:
Multi purpose security tool. |
| 4. BackTrack Live CD :
Linux live CD distribution for Pentesting. |
| 5. LC5 : Tool to
dump hashes and recover passwords for windows users. |
| |
| |
|
|
|